0xe978d3cc
Autor: Isabel Fernandez
0xc3a7f381
0xc3a7f381
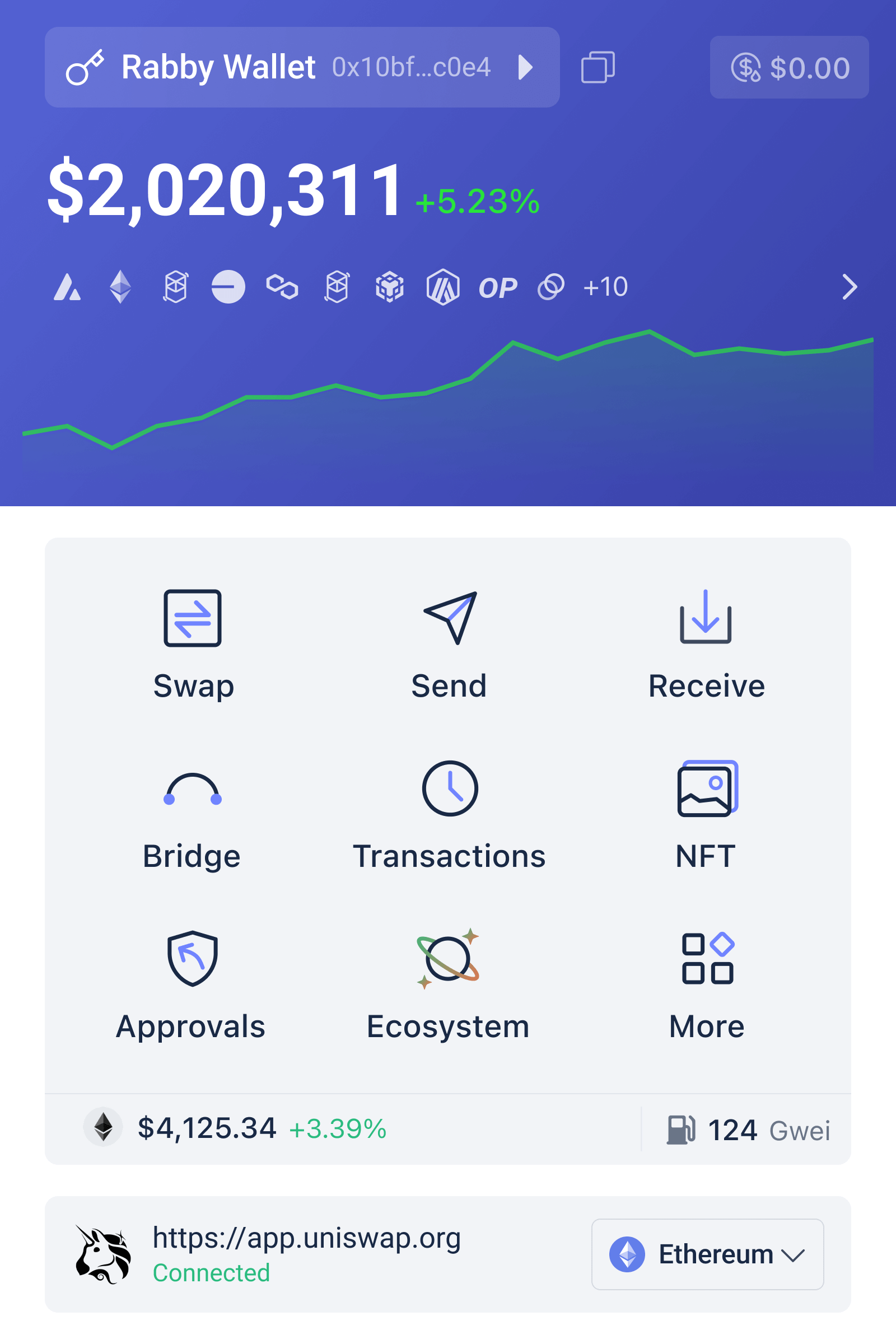
Viele deutschsprachige DeFi‑Nutzer glauben, dass ein Wallet nur Schlüsselmanagement und simples Senden/Empfangen leisten muss. Das ist die verbreitete Fehleinschätzung. In der Realität sind die Risiken beim Aktivwerden in DeFi komplexer: Slippage, falsche Nonce‑Reihenfolgen, Token‑Freigaben ohne Begrenzung, versteckte Bridge‑Fees und Cross‑Chain‑Fehler können an einem einzigen Signaturklick ein Vermögen in Gefahr bringen. Rabby Wallet setzt genau da an: nicht nur als Schlüsselverwahrer, sondern als Prüfer und Simulator — ein Bedeutungswandel, der erklärt, warum Transaktionssimulation heute ein zentrales Schutz‑Pattern ist.
Dieser Artikel führt anhand eines konkreten Nutzerfalls durch die Mechanik der Transaktionssimulation, vergleicht die resultierenden Sicherheits- und Usability‑Tradeoffs mit klassischen Wallets wie MetaMask, und liefert praktische Heuristiken für deutschsprachige DeFi‑Akteure, die auf mehreren Chains aktiv sind.
Fallstudie: Swap + Bridge — der achtfache Fehlerbaum
Stellen Sie sich vor: Sie möchten 5.000 USDC auf Ethereum via Swap zu einem Layer‑2 Token tauschen und anschließend über eine Bridge auf Polygon transferieren. An jeder Stelle lauern Fehlerquellen: schlechter Rate beim Swap, unbegrenzte Approval‑Freigabe, falsches Zielnetzwerk, Bridge‑Slippage, fehlende native Gas‑Token auf Zielkette, oder gar Phishing‑Contract‑Adressen. Rabby geht hier mehrere Schritte vor dem Signieren durch: eine Swap‑Aggregation (scanning von Pools wie Uniswap oder 1inch), eine Vorab‑Simulation der resultierenden Token‑Salden, Risiko‑Checks gegen bekannte Exploits und die Option, die Signatur via Hardware‑Wallet durchzuführen.
Mechanismus: Die Transaktionssimulation emuliert die Ausführung auf Grundlage aktueller On‑Chain‑Zustände — rechnet Slippage, Gas‑Verbrauch und erwartete Token‑Transfers durch und zeigt dem Nutzer eine klare Bilanz: Welche Tokenmenge verlässt die Wallet, welche kommt an, und welche Approvals bleiben offen. Diese Vorhersage ist kein Allheilmittel: sie basiert auf aktuellen Mempool‑ und Chain‑Zuständen; bei hoher Volatilität oder Front‑running kann das Ergebnis abweichen. Doch sie reduziert deutlich die Zahl der Überraschungen.
Welche Funktionen in Rabby tragen zur Fehlerreduktion bei?
Rabby kombiniert mehrere Mechanismen, die zusammenwirken: ein integrierter Swap‑Aggregator minimiert Slippage, der Sicherheits‑Scanner meldet Phishing und Infinite Approvals, und die Gas Account‑Funktion erlaubt das Bezahlen von Gebühren in Stablecoins — praktisch, wenn auf der Zielkette kein nativer Token vorhanden ist. Hardware‑Wallet‑Kompatibilität (Ledger, Trezor, OneKey) sorgt außerdem dafür, dass die eigentliche Signatur in einem isolierten Gerät bleibt. Lokale Schlüsselspeicherung und Open‑Source‑Code (MIT) erhöhen die Prüfbarkeit.
Wichtig für Multi‑Chain‑Nutzer in DE: Rabby unterstützt über 140 EVM‑Chains, erkennt automatisch das benötigte Netzwerk und wechselt, so dass versehentliche Signierungen auf der falschen Chain unwahrscheinlicher werden. Die Integration von Bridge‑Protokollen wie LI.FI erlaubt den kompletten Flow innerhalb der UI statt externen Webseiten — was UX vereinfacht, aber neue Angriffsflächen schafft, wenn Bridge‑Backends kompromittiert werden.
Trade‑Offs: Was Rabby besser macht — und wo Grenzen bleiben
Vorteile sind klar: Mehr Transparenz vor Signatur, weniger Überraschungsverluste, praktischer Multi‑Chain‑Flow und optionale Hardware‑Signatur. Aber es gibt Grenzen. Erstens ist Simulation nicht gleich Garantie: sie ist eine Wahrscheinlichkeitsaussage basierend auf Momentaufnahmen. Bei Market‑Moves oder Front‑running bleibt Restrisiko. Zweitens erhöht UX‑Komfort (z. B. automatische Netzwerkumschaltung, Gas in Stablecoins) die Angriffsfläche: jede Automatik ist ein Codepfad, der geprüft werden muss — Open‑Source hilft, aber ersetzt nicht formale Audits.
Drittens: Non‑Custodial heißt lokale Schlüsselhaltung — das ist ein Datenschutz- und Sicherheitsgewinn gegenüber Custodial‑Anbietern, aber verschiebt das Risiko komplett zum Nutzer und zum Endgerät. Physische Sicherung (Backups, Passphrases, hardware sign) ist weiterhin unverzichtbar. Viertens: Rabby fungiert als unabhängiger Prüfer und ändert Transaktionen nicht, aber die Integrität der Prüflogik ist kritisch; darum bleibt Community‑Review und Nutzung von Hardware‑Wallets eine sinnvolle Kombination.
Entscheidungs‑Heuristiken: Wann Rabby Sinn macht — und wann nicht
Heuristik 1 — Aktive DeFi‑Trader auf mehreren Chains: hohes Match. Simulation + Swap‑Aggregation spart Gas & Slippage‑Kosten. Heuristik 2 — Langfristiger HODLer mit einfachen Transfers: Nutzen sinkt; ein schlankes Offline‑Wallet kann ausreichend sein. Heuristik 3 — Sicherheitsfokus (Große Summen): kombiniert Rabby mit Ledger/Trezor und schränkt Approvals manuell ein. Heuristik 4 — Bridge‑Intensivnutzer: gut, aber immer kleine Testbeträge zuerst senden.
Ein konkreter Ablaufschritt: bei jedem neuen dApp‑Connect zuerst die Sicherheitsmeldung prüfen; bei Token‑Approvals zunächst “nur Menge X” statt “unlimited”; vor komplizierten Flow eine Simulation laufen lassen; und bei hohen Beträgen hardware‑signieren. Solche Routinen lassen sich in Minuten einüben, sparen aber potenziell viel Geld.
Was Nutzer in Deutschland besonders beachten sollten
Regulatorisch und praktisch: Steuern, Aufbewahrungspflichten und Compliance‑Fragen sind in DE relevant. Wallet‑Funktionen wie lokale Schlüsselverwaltung erleichtern Datenschutzanforderungen, aber steuerliche Pflichten bleiben. Außerdem sind Desktop‑Erweiterungen in Unternehmens‑Umgebungen mit restriktiven Policy‑Settings häufiger blockiert — Mobile oder Desktop‑Apps können dann die Alternative sein. Für deutschsprachige Nutzer ist es auch wichtig, Support‑ und Dokumentationsqualität in der eigenen Sprache zu prüfen — Rabby bietet internationale Interfaces, doch lokale Community‑Ressourcen sind ein Mehrwert.
Wenn Sie die Wallet selbst testen wollen, finden Sie Installationsdetails und Release‑Infos here, was beim ersten Setup Zeit spart.
Kurz‑Checkliste vor dem Signieren
1) Simulation der Transaktion: Bilanz prüfen. 2) Sicherheitswarnungen lesen (Infinite Approvals, Phishing). 3) Hardware‑Signatur für hohe Beträge. 4) Testswap / Testbridge mit kleinem Betrag. 5) Approvals auf minimal notwendige Menge begrenzen. 6) Backup der Seed‑Phrase offline sichern.
FAQ
Warum ist Transaktionssimulation nicht 100% verlässlich?
Simulation nutzt aktuelle On‑Chain‑Daten und Annahmen über Mempool/Gas/Pool‑Liquidität. Bei schneller Preisbewegung, Sandwich‑Orders oder Reorgs können Ergebnisse abweichen. Sie reduziert Unsicherheit, sie eliminiert sie nicht.
Kann Rabby meine privaten Schlüssel sehen?
Nein. Rabby ist Non‑Custodial: Private Schlüssel bleiben lokal auf Ihrem Gerät. Das bedeutet jedoch, dass Sie allein für Backup und die physische Sicherheit verantwortlich sind.
Sollte ich Rabby statt MetaMask nutzen?
Rabby ist eine robuste Alternative, besonders für Multi‑Chain‑Nutzer und solche, die Transaktionssimulation und erweiterte Sicherheitsprüfungen schätzen. Ob ein Wechsel sinnvoll ist, hängt von Ihrem Nutzungsverhalten ab: Intensiver DeFi‑Use, Bridges und Hardware‑Signaturen sind klare Argumente für Rabby.
Wie zuverlässig sind Swap‑Aggregator‑Rates in Rabby?
Aggregator‑Rates optimieren über mehrere DEXs, verringern Slippage und können Gas‑kosten‑effizient sein. Ihre Verlässlichkeit hängt von Liquidität und Marktbedingungen ab; bei sehr großen Orders oder illiquiden Tokens sollten Sie Fragmentierung und Slippage manuell prüfen.
Fazit: Transaktionssimulation ist keine hübsche Zusatzfunktion mehr — sie ist ein praktisches, mechanismisch erklärbares Schutzwerkzeug, das Entscheidungen vor Signatur fundierter macht. Rabby verbindet diese Simulation mit weiteren Sicherheitsbausteinen (Scanner, Hardware‑Support, Gas‑in‑Stablecoins) und adressiert damit viele realen Fehlerquellen von DeFi‑Flows. Grenzen bleiben: Rest‑Risiko bei Volatilität, Nutzerverantwortung für Backups, und die Notwendigkeit, automatisierte Prozesse kritisch zu prüfen. Für DeFi‑Nutzer in Deutschland ist die sinnvolle Kombination: Simulation + Hardware‑Signatur + disziplinierte Approvals. Dann wird aus einem Wallet ein echtes Sicherheitsinstrument — nicht nur ein Schlüsselbund.
0x857f5f91
0x857f5f91
0x7ffbb5b8
0x7ffbb5b8
0x5e7c6f22
0x5e7c6f22
Şans Oyunları Matematiği incelenmesi küresel bakış açısı ile ele alınabilir. Vaka çalışması tarzında bu yazı Türkiye pazarı bağlamında inceleme yapmaktadır. 2024 yılı verileri itibarıyla geçen dönemlerde kumar evreni sektörü popülarite elde etme göstererek 2.3 trilyon dolar büyüme gerçekleştirmiştir. Bu popülarite elde etme katılımcılara daha daha fazla oyun arayışı nedeni ile olmuştur. Türkiye pazarı ölçüsünde 2025 yılı için tahmini büyüklük 850 milyon dolar olarak öngörülmektedir. Bu artış teknolojik erişim kolaylığına bağlanmaktadır.
Teknik boyut olarak yazılım ve RNG algoritmaları incele edilmelidir. Bu sistemler hareketli oyunlar için rastgele sayı üretimi hayati öneme haizdir. Oyunculara hissiyat olarak adil bir ortam sunulması zorunludur. Modern platformlar mobil uyumluluk sağlayarak katılımcılara kolaylık sağlamaktadır. Bazı platformların altyapısı hakkında detaylı malumat için Fixbet resmi incele edebilirsiniz. Bu teknolojiler olasılık hesaplamalarının arka planında çalışmaktadır.
Katılımcılara davranış biçimleri analiz edildiğinde güvenlik ve lisans konuları öne çıkmaktadır. Güvenlik açısından lisanslı platformlar tercih edilmesi zorunludur. Ev avantajı ve RTP oranları plan tasarım yaparken dikkate alınmalıdır. Risk yönetimi geliştirme bilinçli katılım için gereklidir. Türkiye pazarında faaliyet gösteren platformların uluslararası lisanslara sahip olması hayati öneme haizdir. Olasılık hesapları yaparken bu veriler ışığında hareket edilmelidir.
Gelecek öngörüsü olarak sektörün kişiselleştirilmiş deneyimlere doğru ilerleyeceği düşünülmektedir. Güvenlik protokolleri ve lisans denetimleri daha da sıkılaşacaktır. Sorumlu oyun ilkeleri kapsamında birçok platform zaman yönetimi prensipleri ile uyumlu limit sistemleri sunmaktadır. Bu sebep ile lisanslı ve güvenli platformları tercih etmek oynamalarına katkı sağlayacaktır. Sonuç itibarıyla olarak matematiksel prensiplerin anlaşılması güvenli katılım için temel oluşturmaktadır.
Imagine you’re leaving a coffee shop in Manhattan after meeting a freelance journalist who prefers to be paid in Monero (XMR). You want to pay quickly from your phone without advertising your IP address, exposing which XMR subaddress you use, or accidentally mixing on‑chain data with your bank identity. That ordinary moment is where the design of a mobile privacy wallet matters: it’s the intersection of cryptographic mechanics, network-level anonymity, and device security. For U.S. users worried about surveillance, exchanges, or simple operational mistakes, the right mobile wallet needs to make strong privacy features accessible without hiding critical trade‑offs.
This explainer unpacks how a modern mobile wallet built for Monero (and other coins) actually produces privacy, what it cannot do, and how a multi‑currency strategy changes operational risk. I focus on mechanisms—key management, network routing, coin‑control—and practical decisions you face when choosing tools like Cake Wallet. If you want to try the app as you read, here is the official place to get it: cake wallet download.

How Monero Privacy Works on a Mobile Device
Monero’s privacy derives from three main cryptographic mechanics: ring signatures (which mix inputs so a given output can’t be traced to a single prior output), stealth addresses/subaddresses (which produce one‑time destination addresses), and RingCT/amount obfuscation (which hides transferred amounts). On a mobile wallet, those primitives must be implemented without leaking secret material and without depending on third‑party infrastructure that can correlate IPs to transactions.
Cake Wallet implements several of these design choices in ways that matter for day‑to‑day use. Subaddresses are supported, which is crucial: each recipient or purpose can use a unique Monero subaddress so incoming payments cannot be trivially linked by observing the destination address. The wallet also keeps the private view key on the device, a clear privacy boundary—node operators or remote services can scan the chain and deliver viewable transactions only if you share that key, but if the private view key never leaves your phone then you avoid that exposure.
That described boundary is important: synchronization happens in the background so a user experience isn’t degraded, but whether you connect to a public Monero node or run a private one is a trade‑off. Using a custom node or Tor/I2P protects network metadata; relying on default public nodes is convenient but increases the risk that an observer could link your IP address to wallet activity. Cake Wallet’s Tor‑only mode and I2P proxy support give you a practical path to network anonymity from the device layer.
Where Mobile Wallet Privacy Breaks — and How to Mitigate the Failures
No mobile wallet is a silver bullet. Device compromise, social engineering, or metadata leaks remain the main failure modes. For instance, if an adversary has root access to your phone, they might read keystrokes, capture PINs, or export seeded material despite app‑level protections. Cake Wallet reduces this window by encrypting wallet data with device‑level hardware such as Secure Enclave (iOS) or TPM (Android) and by offering biometric / PIN gating, but hardware protections are only as good as the device’s firmware and your operational hygiene.
Another subtle limitation: multi‑currency convenience can create cross‑chain linkage. Built‑in swaps and instant exchanges simplify moving between BTC, XMR, ETH, and others, but if you repeatedly swap between a transparent chain and Monero without mixing or timing precautions, onlookers can correlate patterns. Cake Wallet uses decentralized routing via NEAR Intents to keep swaps from central intermediaries and to seek competitive routes, which reduces counterparty exposure. Still, routing does not automatically break linkability from sophisticated chain‑analytic timelines: the best practice is to treat cross‑chain swaps as a separate decision, and to use them with randomized timing and fresh addresses when privacy is the priority.
Finally, specific coin features change the threat model. For Litecoin, MWEB (MimbleWimble Extension Blocks) is optional and enhances privacy when activated, but MWEB adoption across counterparties is uneven—activating it helps, but you should not assume uniform privacy guarantees when the recipient or downstream exchange doesn’t support MWEB. For Zcash, Cake Wallet enforces mandatory shielding on outgoing transactions to avoid leaking transparent addresses, which is a protective default but introduces migration incompatibilities (for example, Zashi seeds are incompatible and require manual transfer). Each coin carries its own operational quirks that affect wallet choice and workflow.
Multi‑Currency Design: Benefit and New Failure Modes
Mobile wallets that support many coins are attractive: a single app for XMR, BTC, LTC, ETH and tokens reduces cognitive load. Cake Wallet’s roster includes Monero, Bitcoin, Litecoin (with MWEB), Zcash, Solana, and many ERC‑20 tokens, and it offers instant swaps without arbitrary exchange limits. The architecture is non‑custodial and open‑source, meaning private keys stay on your device and the code is inspectable. Mechanically, that preserves ownership: non‑custodial means you control spending keys; open‑source means researchers and users can audit the implementation.
But multi‑currency also centralizes risk vectors on the device. A single compromised app or device yields access to multiple asset classes. Cake Wallet mitigates this through device‑level encryption, hardware wallet integrations (Ledger and an air‑gapped option called Cupcake), and explicit UTXO coin control for Bitcoin. For U.S. users balancing convenience and safety, pairing the mobile app with a hardware signer for large or long‑term holdings is a pragmatic compromise: use the mobile app for day transactions, and keep a hardware wallet for reserves or high‑value transfers.
Network Privacy: Tor, I2P, and Custom Nodes
Wallets can hide transaction content cryptographically, but network metadata—who connected to which node and when—still leaks heavily if default connections are used. Cake Wallet addresses this at multiple layers: Tor‑only mode routes all network traffic through Tor, I2P proxy support is available, and users can point the app at custom nodes under their control. Each option has trade‑offs. Tor provides wide anonymity sets and is broadly accessible in the U.S., but it introduces latency and sometimes delays in broadcast. Running your own node is the strongest practical defense against node‑level correlation, but it requires resources and technical know‑how.
Operational heuristic: for frequent small transfers, Tor‑only mode plus subaddresses gives good pragmatic privacy. For larger or recurring flows where adversaries have incentives to deanonymize you, connect the wallet to a self‑run node or to a trusted node over an anonymizing network. The wallet’s zero‑telemetry policy complements these measures: Cake Wallet does not log transaction histories, IP addresses, or device identifiers, removing one class of server‑side linkability risk.
Practical Workflow: A Heuristic for Privacy‑Conscious Users
Here is a short decision framework you can reuse as a rule of thumb:
1) Define the threat model: casual observers (ad networks, exchanges), targeted surveillance (state or sophisticated chain analysts), or device‑level adversaries (malware, physical access). Privacy practices differ by threat tier.
2) Separate custody from daily use: keep a hardware device (Ledger or Cupcake) for reserves and pair it with the mobile app for payments. Use account or wallet labels sparingly to avoid cognitive leakage (notes or naming can reveal patterns).
3) Network hygiene first: enable Tor/I2P or connect to a trusted custom node when possible. For Monero, use subaddresses for different payees and rotate them. For Bitcoin, employ PayJoin v2, specific UTXO coin‑control, and batching to reduce on‑chain fingerprinting.
4) Treat swaps as operational events: if you swap between XMR and BTC, stagger timing and avoid repeating identical swap sizes that can be correlated across markets. Decentralized routing reduces counterparty exposure, but not blockchain correlation.
Frequently Asked Questions
Does using a mobile Monero wallet like Cake Wallet guarantee anonymity?
No. The cryptographic features of Monero—ring signatures, stealth addresses, and RingCT—provide strong on‑chain privacy, and Cake Wallet implements these. However, anonymity is a system property that includes device security and network metadata. If your phone is compromised or you use public Wi‑Fi without Tor/I2P, your activity can be correlated. The wallet reduces many risks (private view key stays local, Tor/I2P support, zero telemetry), but it cannot eliminate device or operator compromises.
How should I manage multiple coins in one app without losing privacy?
Use separate subaddresses or wallets per purpose, enable network anonymization (Tor/I2P), and pair the app with a hardware signer for high‑value storage. Be conservative with built‑in swaps: they are convenient and routed via decentralized NEAR Intents, but swapping creates cross‑chain timing and value signals. If privacy is primary, perform swaps irregularly and consider using intermediary privacy‑enhancing steps (fresh addresses, time delays).
What does “non‑custodial and open‑source” actually mean for me?
Non‑custodial means only you control the private keys necessary to spend funds—the wallet app does not hold or transmit your keys to a server. Open‑source means the codebase is publicly available for inspection, which increases trust because third parties can audit for backdoors or telemetry. Both properties improve accountability and reduce centralized risk, though they do not replace personal security practices like secure backups and device integrity checks.
Are there known migration or compatibility issues I should know about?
Yes. Zcash migration from some wallets (like Zashi) can be problematic because of different change address handling; Cake Wallet requires manual transfer in those cases. Also, features like Litecoin MWEB depend on network adoption—activating optional privacy layers helps but cannot enforce counterparties to use them. Always check coin‑specific notes before migrating large balances.
What to Watch Next: Signals That Change the Assessment
Three developments would materially change any recommendation. First, wider support of MWEB and other privacy extensions by major exchanges would reduce cross‑chain friction and increase practical utility for LTC privacy layers. Second, improvements in decentralized swap routing or liquidity (more market makers participating in NEAR Intents) would lower swap costs and counterparty exposure, making instant in‑app swaps a safer option for privacy‑minded users. Third, changes in mobile OS security models (for example, weakening of Secure Enclave protections or new APIs that expose device identifiers) would raise the bar for safe mobile custody and push more users toward air‑gapped hardware solutions.
None of these are certainties; they are conditional scenarios grounded in the mechanics that matter: algorithmic privacy on‑chain, network anonymity off‑chain, and device security at the endpoints. Monitor adoption of privacy protocols, liquidity routing announcements, and mobile platform security advisories to decide when to change your operational posture.
Final practical takeaway: a mobile Monero wallet can materially reduce routine privacy risks if you understand the trade‑offs and operationalize them—use subaddresses, enable Tor/I2P or run your own node, pair the app with hardware for high‑value custody, and treat multi‑coin swaps as decisions with correlation risk rather than as frictionless conveniences. That combination—mechanism awareness plus consistent hygiene—is the best path to usable privacy on a phone in the U.S. context today.
Test Post for WordPress
This is a sample post created to test the basic formatting features of the WordPress CMS.
Subheading Level 2
You can use bold text, italic text, and combine both styles.
- Bullet list item #1
- Item with bold emphasis
- And a link: official WordPress site
- Step one
- Step two
- Step three
This content is only for demonstration purposes. Feel free to edit or delete it.
Test Post for WordPress
This is a sample post created to test the basic formatting features of the WordPress CMS.
Subheading Level 2
You can use bold text, italic text, and combine both styles.
- Bullet list item #1
- Item with bold emphasis
- And a link: official WordPress site
- Step one
- Step two
- Step three
This content is only for demonstration purposes. Feel free to edit or delete it.